In the first part of the article we simply deployed the vCenter 5.5 VM from the OVF file – vCenter Server 5.5 Linux Appliance – Install/config ![]() . Fast and efficient. While we successfully integrated the VCSA to the Windows domain and we could see the computer account in the AD, we still had to log in with the default VMware credentials (root/vmware) to the VCSA. Now it's time to finish the configuration and allows the possibility to use Single Sign-On and centralized logins by leveraging Windows AD. So that's why this article about VCSA 5.5 Installation and configuration – part 2.
. Fast and efficient. While we successfully integrated the VCSA to the Windows domain and we could see the computer account in the AD, we still had to log in with the default VMware credentials (root/vmware) to the VCSA. Now it's time to finish the configuration and allows the possibility to use Single Sign-On and centralized logins by leveraging Windows AD. So that's why this article about VCSA 5.5 Installation and configuration – part 2.
VCSA 5.5 Installation and configuration – The configuration steps:
01. Login to the VCSA appliance with login: [email protected] pass: vmware (this is the default domain which is created by default – it's built-in the VCSA 5.5)
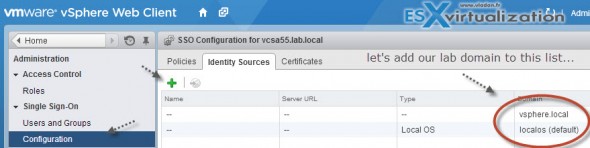
Go to Administration > Single Sign-On > Configuration
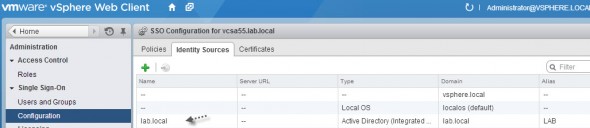
By default you see the default vSphere.local domain and localOS authentication that are those default ones.
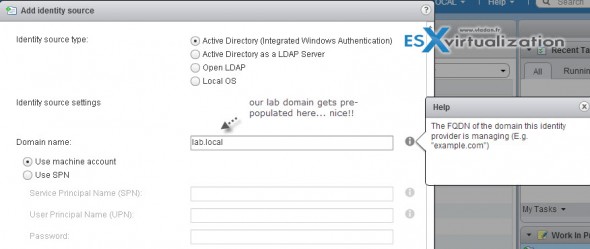
02. Click the Plus sign > Select Active Directory (integrated Windows Authentication)
You'll see a screen like the one below, where when you select the radio button for the AD authentication (first option) my lab domain got pre-populated there
Now when this done you should end up with a screen like the one below. An additional Identity source has been added – our lab.local domain. Good, but that's not finish. It still require one more step.
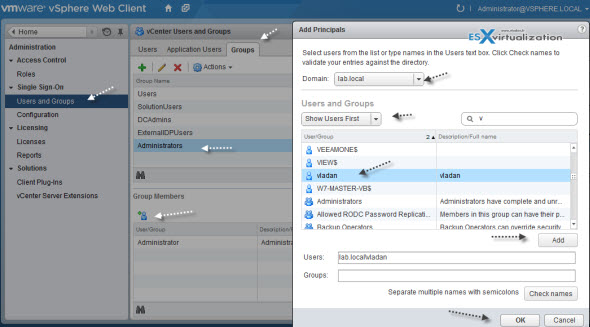
03. Click the Groups TAB, then Select Administrators group. Then see the image for additional steps. I'm using my own AD account called Vladan, which is member of the Domain Administrators group in my Windows domain.
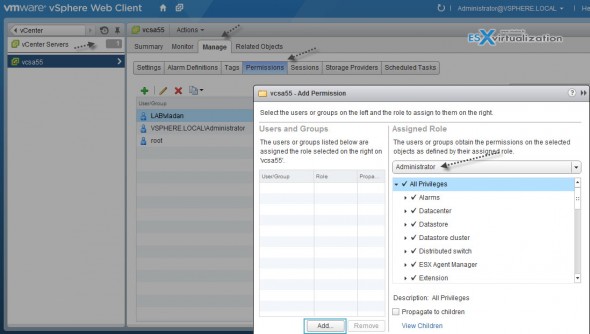
04. Next you have to give that user a permission to administer the top level objects in vCenter. You'll have to:
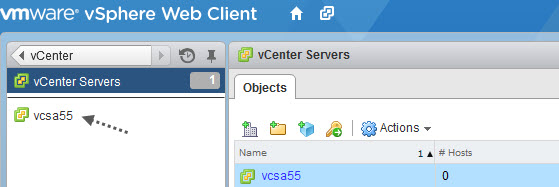
click vCenter > Select vCenter server > click again on the name of your vcenter server (see screenshot)
Next you'll see a view like this. You click on Manage TAB > Permissions > Click the green Plus button and Click the Add button.
You can then select from the drop-down list your domain and choose the user you want to give him a permission. After validation, the user appears like this:
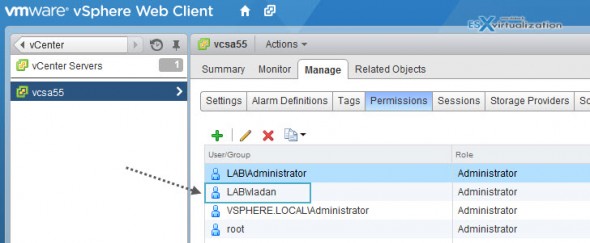
Once done, you can log out, and log back in with [email protected] as an account… -:)
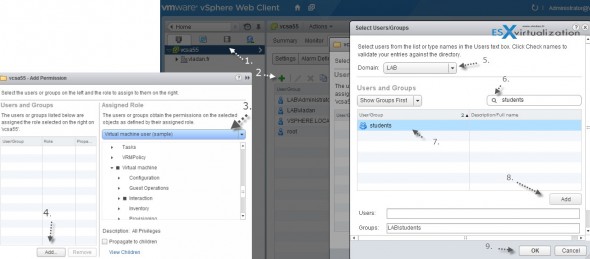
Now what if you want to give a less privileges to a user or a group of users?
You can of course add not only users, but also groups from AD. And you can add users/groups with less privileges if you want them just to manage some VMs. For example I've created (in my AD) a group called Students and put an AD account called student. I want this user only to use a VM, but nothing else..
Now I can easily attach this group to an existing template (virtual machine user) .Just click the High resolution graphic to see the details. I think you get the point…
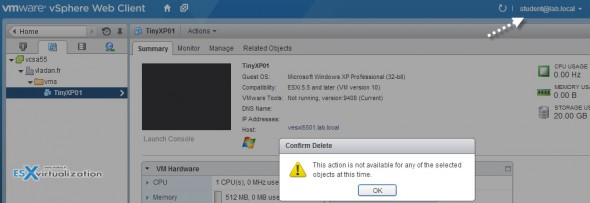
And we can verify that the user cannot delete our VM….
Now, this is not new in vSphere 5.5. The administration of users, groups, and roles is part of the vSphere since the beginning. But the web based interface make doing things a slightly different ways, so I don't thinks its a bad to re-hash a bit…-:) Plus, there is still new folks which are just starting with IT, virtualization, and learning more about VMware techologies. That's why also this post was born.
Feel free to subscribe to our RSS feed or follow me on Twitter: @vladan
Did you like this post? SHARE it through any of those social networks -:).


is vcenter 5.5 available to download right now?
Hi,
I’ve just installed vcenter 5.5 appliance and when trying to configure users from AD DS (on SSO -> Users and Groups, click on Groups then Administrators and on bottom i’ve icon with plus) got screen Add Principals, and when changing domain to my AD DS domain i have empty list and got alert: Cannot load the users for the selected domain.
Why? What i’ve done wrong?
Difficult to say. Normally it should populate users and groups from AD. Have you logged in as [email protected] ?
Hey arucard
I had the exact same message. “Cannot load the users for the selected domain.”
In my case the first DNS server entry was my firewall. Which does normally route dns request to my Active Directory pretty fine to the domain DNS servers… but not in this case.
To solve the issue I set only the Active Directory DNS servers in the network settings of my VCA.
Best regards
Yvan
Hello arucard,
for me it was the same, go on again with users and user groups and then choose your domain. With the filters I’ve found my account. Then simply go again to the Administrators group, and then you find yourself when you select the domain. However, I can not !!! login with an AD user on WebClient. He says the password is incorrect. Is the syntax wrong?
The post got updated with more screenshots and more details as I figured out that it’ll give you ALL necessary details from A-Z. Hope it helps…
Is there any way to invoke some Windows vCenter 5.1 configurations like resource pools, vDS and other important “time eating” things? If external SQL is/will be supported that could be done, but how to make conversion to embeded DB?
Not quite sure what you’re referring to. The only limitations that’s not supported with VCSA is linked mode. Also vCenter server Heartbeat isn’t supported with VCSA. VUM has to be installed on separate Windows box, the same for View composer. ANd SSPI (security support provider interface) – Microsoft Windnows API used to perform authentication against NTLM or Kerberos.
The limits (soft) of 100 hosts and 3000 VMs has also been confirmed.
Do not forget to create PTR record for your domain controller:
<a href="http://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=2033742"
Yes, solid DNS architecture must be in place before the deployment, as I’m poining it out in the Part 1: http://www.vladan.fr/vcenter-server-appliance-5-5/
Thanks.
Thank you Vladan.
I could not retrieve the list of domain users, until I added the PTR record of my Domain Controller. You really helped a lot understanding the way it works.
Thank you Petros and Vladen. The last piece of he puzzle finally solved. Reverse Lookup zone and DC PTR records did the trick.
Excellent article!!!
Excellent article really help a lot for me. Keep up the great work!!!
First let me thank you for this article. It is excellent and succinct.
My DNS was correct, and I still experienced the error, “Cannot load the users for the selected domain.”
Here is what I did to resolve my problem:
1. For Identity Source, use “Active Directory as a LDAP Server.”
2. Configure the following identity source settings:
For example, if my domain name is
example.com, I would use the following:Base DN for users:
dc=example,dc=comDomain name:
example.comDomain alias:
EXAMPLEBase DN for groups:
dc=example,dc=comPrimary server URL:
ldap://:389Username:
[email protected]