Today we will tackle VCP6-DTM Objective 1.4 – Install Horizon (with View) Security Server. VCP6-DTM Study Guide continues, you could possibly check the VCP6-DTM page where we're moving forward to not only cover Horizon View, but also VMware Mirage and Horizon Workspace.
All the topics from the VMware blueprint will be covered. Check the VCP6-DTP Study Guide Page for all topics. The certification exam is a necessity for VMware admins willing to get deeper knowledge on Horizon View and DR products like Mirage or Workspace and get certified in this track. It's the second step forward VCAP, VCIX or VCDX in the destkop certification tree.
Let's have a look what we will cover today:
Horizon View Knowledge
- Determine required firewall rules
- Configure Horizon View security server pairing
- Navigate the View Connection server installation wizard
Horizon View PDF Documentation Tools
- Horizon View Installation Guide
- Horizon View Security Guide
- Horizon View Administration Guide
- Horizon View Administrator
Determine required firewall rules
If you choose to install HTML Access with View Connection Server, the installer configures the VMware Horizon View Connection Server (Blast-In) rule in Windows Firewall to open TCP port 8443, used by
HTML Access (Previously called VMware Blast …. )
View connection server firewall requirements (from the Installation guide p.58):
- TCP 4001 Standard and replica
- TCP 4100 Standard and replica
- TCP 8009 Standard and replica
- HTTP TCP 80 Standard, replica, and security server
- HTTPS TCP 443 Standard, replica, and security server
- PCoIP TCP 4172 in;
- UDP 4172 both directions Standard, replica, and security server
- HTTPS TCP 8443 Standard, replica, and security server. After the initial connection to View is made, the Web browser on a client device connects to the Blast Secure Gateway on TCP port 8443. The Blast Secure Gateway must be enabled on a security server or View Connection Server instance to allow this second connection to take place.
- HTTPS TCP 8472 Standard and replica For the Cloud Pod Architecture feature: used for interpod communication.
- HTTP TCP 22389 Standard and replica For the Cloud Pod Architecture feature: used for global LDAP replication. HTTPS TCP 22636 Standard and replica For the Cloud Pod Architecture feature: used for secure global LDAP replicatio
During the installation, Horizon View will prompt you to open Windows firewall ports automatically. This is optional step.
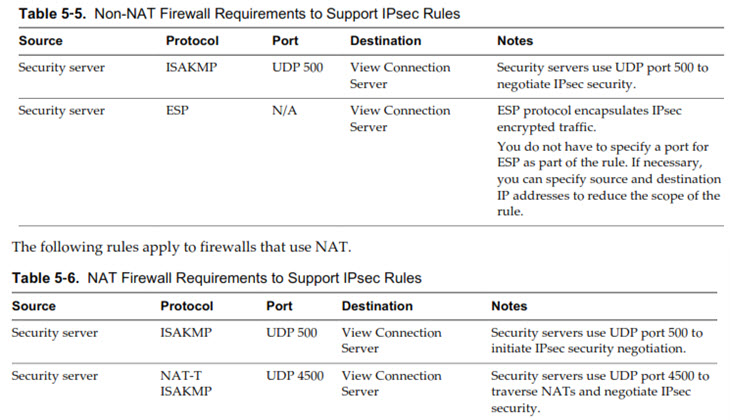
Back-End firewall config between Security servers and View connection server instances – If your network has a back-end firewall between security servers and View Connection
Server instances, you must configure certain protocols and ports on the firewall to support IPsec. If not, the data sent between a security server and View Connection Server instance will fail to
pass through the firewall.
By default, IPsec (highly recommended to use IPsec) rules (allowing bidirectional traffic) govern the connections between security servers and View Connection Server instances. To support IPsec, the View Connection Server installer can configure Windows firewall rules on the Windows Server hosts where View servers are installed. For a back-end firewall, you must configure the rules yourself.
Configure Horizon View security server pairing
The configuration of the pairing password is done through the view admin UI.
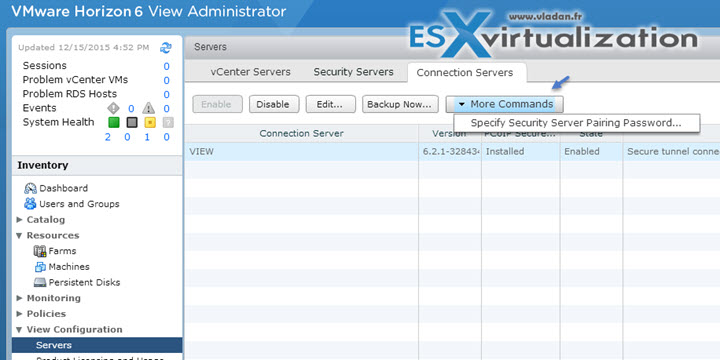
Select View Configuration > Servers > Connection Servers > More commands > And then Specify Security Server Pairing password.
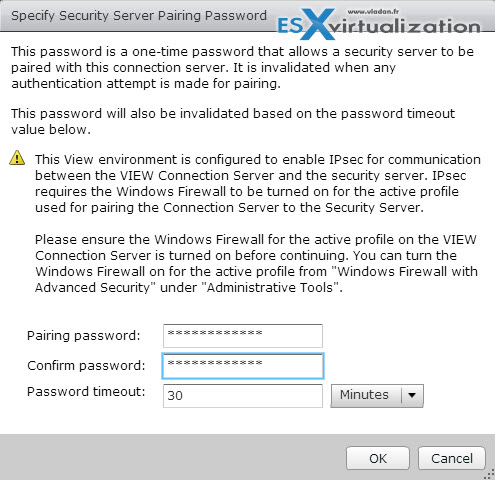
And then… as you can see you can enter the password but also specify the time during which the password stays valid. By default it's 30 min. You can change the value or from the dropdown select hours instead of minutes.
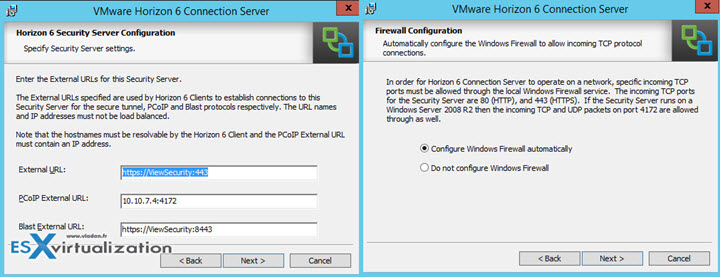
Navigate the View Connection server installation wizard
A security server is an instance of View Connection Server that adds an additional layer of security between the Internet and your internal network. You can install one or more security servers to be connected to a View Connection Server instance.
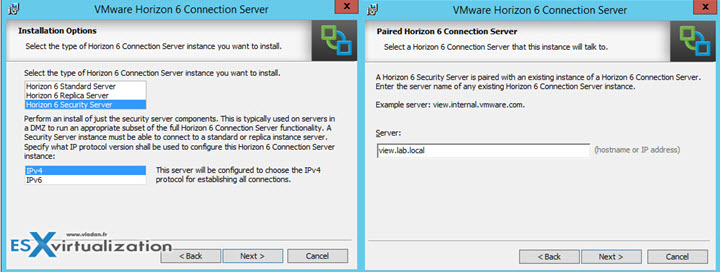
Here you can enter the pairing password which stays active only 30 min by default. We saw it above where to configure it…

The external URL for PCoIP and Blast protocol access…
And then last two screens here…
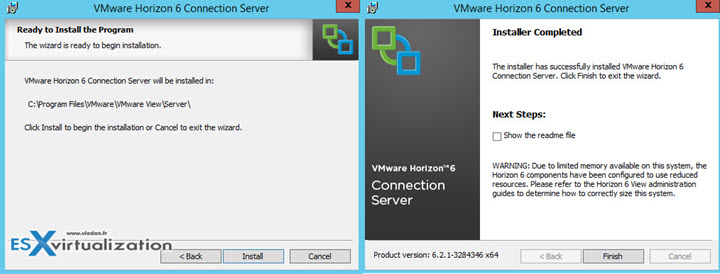
That's about it concerning the security server. You should definitely look at the requirements we have enumerated in VCP6-DTM Objective 1.5 – Prepare Environment for Horizon (with View).
