Today's post will describe and walks you through some VMware ESXi host security features and options. VCP6.7-DCV Objective 7.4 – Configure host security is today's topic which is part of the VMware official blueprint you need to follow when studying towards VCP-DCV 2019 certification. The exam's name is Professional vSphere 6.7 Exam 2019.
You have several ways to become VCP certified. You can still pass VCP6.5-DCV: VMware Certified Professional 6.5 – Data Center Virtualization exam (our VCP6.5-DCV Study Guide Page ) and still obtain the latest VCP-DCV 2019 certification.
As being said, we still follow VMware blueprint and all topics you can find on our VCP-DCV 2019 Study Guide page. The work in progress page gets updated almost daily. Check back soon.
The ESXi hypervisor architecture has many built-in security features such as CPU isolation, memory isolation, and device isolation. You can configure additional features such as lockdown mode, certificate replacement, and smart card authentication for enhanced security.
Risks to the hosts are mitigated out of the box as follows:
- ESXi Shell and SSH are disabled by default.
- Only a limited number of firewall ports are open by default. You can explicitly open additional firewall ports that are associated with specific services.
- ESXi runs only services that are essential to managing its functions. The distribution is limited to the features required to run ESXi.
- By default, all ports that are not required for management access to the host are closed. Open ports if you need additional services.
- By default, weak ciphers are disabled and communications from clients are secured by SSL. The exact algorithms used for securing the channel depend on the SSL handshake. Default certificates created on ESXi use PKCS#1 SHA-256 with RSA encryption as the signature algorithm.
- A Tomcat Web service is used internally by ESXi to support access by Web clients. The service has been modified to run only functions that a Web client requires for administration and monitoring. As a result, ESXi is not vulnerable to the Tomcat security issues reported in broader use.
- VMware monitors all security alerts that can affect ESXi security and issues a security patch if needed.
- Insecure services such as FTP and Telnet are not installed
This guide is available as Free PDF!
Free Download at Nakivo – VCP6.7-DCV Study Guide.
You can tighten security on hosts further by:
- Enabling/Disabling services in the ESXi firewall
- Change default account access
- Adding a VMware ESXi host to a directory service (Microsoft AD or other LDAP capable)
- Apply permissions to the ESXi hosts using host profiles
- Enable Lockdown Mode
- Control access to hosts (DCUI/Shell/SSH/MOB) – via console or vCenter.
Harden ESXi hosts
Only a limited set of services runs by default on each ESXi host.
- ESXi Shell and SSH are disabled by default.
- You can configure additional features such as lockdown mode, certificate replacement, and smart card authentication for enhanced security.
- An ESXi host is also protected with a firewall. You can open ports for incoming and outgoing traffic as needed but should restrict access to services and ports.
- Using the ESXi lockdown mode and limiting access to the ESXi Shell can further contribute to a more secure environment.
- Hosts are provisioned with certificates that are signed by the VMware Certificate Authority (VMCA) by default.
- You might consider using UEFI Secure Boot for your ESXi system.
- Join ESXi hosts to an Active Directory (AD) domain to eliminate the need to create and maintain multiple local user accounts. Using AD for user authentication simplifies the ESXi host configuration, ensures password complexity and reuse policies are enforced and reduces the risk of security breaches and unauthorized access. (Note: if the AD group “ESX Admins” (default) exists then all users and groups that are assigned as members to this group will have full administrative access to all ESXi hosts the domain.)
- Use ESXi lockdown mode – Enabling lockdown mode disables direct access to an ESXi host requiring the host be managed remotely from vCenter Server. Two modes available (normal and strict). Tip: What is ESXi Lockdown Mode? Users on the Exception Users list can access the host from the ESXi Shell and through SSH if they have the Administrator role on the host and if these services are enabled. This access is possible even in strict lockdown mode. Leaving the ESXi Shell service and the SSH service disabled is the most secure option
- ESXi.set-shell-timeout – sets a timeout to limit how long the ESXi shell and SSH services are allowed to run.
Check the VMware Security Hardening guides at VMware Blog.
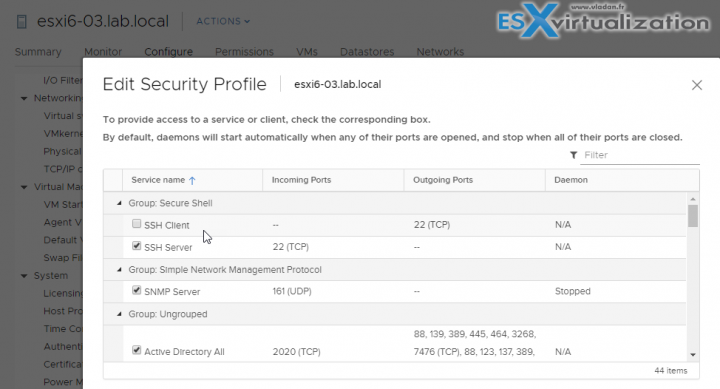
Enable/Configure/Disable services in the ESXi firewall
For each ESXi host, you can create firewall rules.
Connect via vSphere web client > Configure > System > Firewall section > Edit > Select Rule > Enable/disable.
Select the rule sets to enable, or deselect the rule sets to disable. You can change startup policy to have a particular service started with the host or by port usage. Some services allows configuring IP address from which connections are permitted.
Check which services are active
esxcli network firewall ruleset list
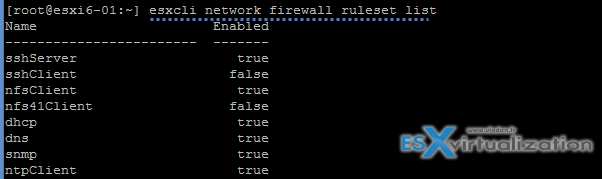
Open firewall port via CLI:
esxcli network firewall ruleset set -e true -r httpsClient
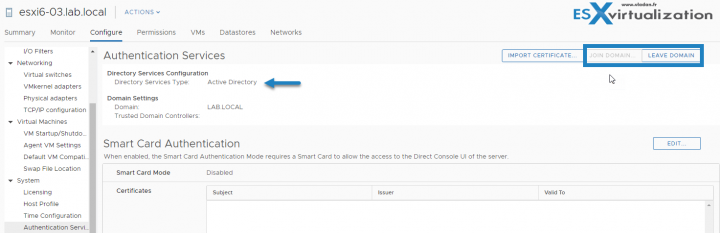
Add an ESXi Host to a directory service
You can configure a host to use a directory service such as Active Directory to manage users and groups. When you add an ESXi host to Active Directory, the DOMAIN group ‘ESX Admins’ is assigned full administrative access to the host if it exists.
A special AD group named “ESX Admins” shall be manually created before a host is joined to Microsoft AD. Why? Because like this All members of this group (ESX admins) are automatically assigned to the Administrator role on the host when this host is joined to an AD. If not the permissions have to be applied manually.
Select your host > Configure > System > Authentication Services > Join Domain > Enter your Microsoft domain name > Use a user and password who has permissoin to join the host to the domain > Click OK.
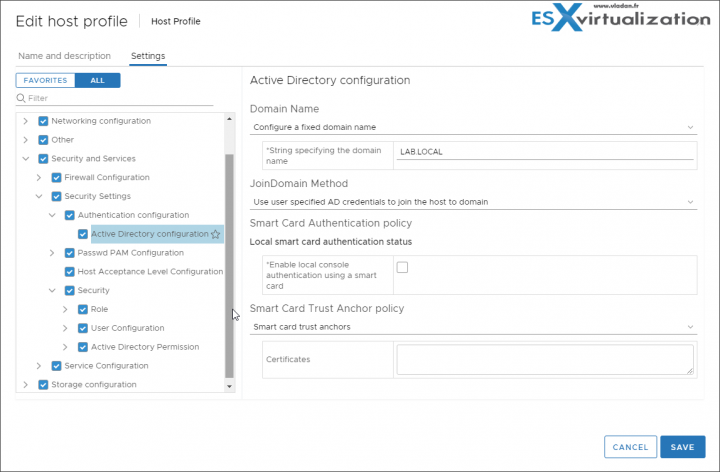
Apply permissions to ESXi Hosts using Host Profiles
Host profiles allow you to “standardize” configurations for ESXi hosts and automate compliance for settings you have set on a reference host. Host profiles allow you to control many aspects of host configuration including memory, storage, networking, and so on. But most importantly, it's possible to apply the same security settings for all hosts within a cluster for example, without configuring those host after host.
In some cases, host profiles can be also useful when for example you need to reset esxi root password on a host.
- Click the host profile > Click Configure > Edit Host profile
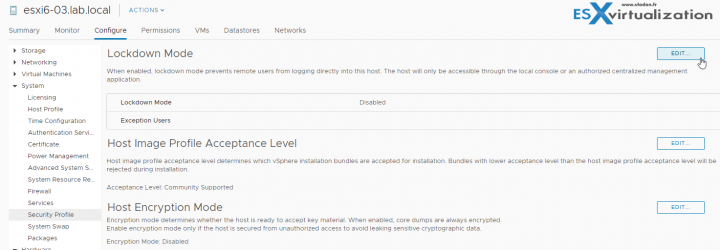
Enable Lockdown Mode
Lockdown Modes:
- Disabled – Lockdown mode is disabled.
- Normal – The host can be accessed through vCenter Server. Only users who are on the Exception Users list and have administrator privileges can log in to the Direct Console User Interface. If SSH or the ESXi Shell is enabled, access might be possible.
- Strict – The host can only be accessed through vCenter Server. If SSH or the ESXi Shell is enabled, running sessions for accounts in the DCUI.Access advanced option and for Exception User accounts that have administrator privileges remain enabled. All other sessions are terminated. DCUI is stopped.
Select your host > Configure > System > Security Profile > Lockdown mode > Edit.
Accounts in the Exception User list for lockdown mode who have administrative privileges on the host. The Exception Users list is meant for service accounts that perform very specific tasks. Adding ESXi administrators to this list defeats the purpose of lockdown mode.
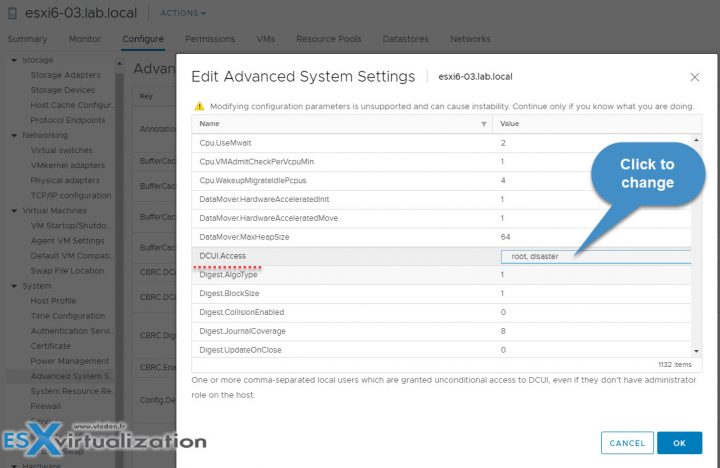
Where to add an account to the Exception Users list?
You’d have to first create a local ESXi user and then specify this advanced settings on per-host base. So in my case, I created a sample local ESXi user called “disaster” through ESXi host client which is a local ESXi user.
So in order to modify the Exception users list, you’ll have to use the vSphere HTML5 client of vSphere Web Client. To access this setting you Select your host > System > Advanced System Settings > within the list find the DCUI.Access > click to add another local ESXi user there. The root user is already present there by default.
The exception users can only perform tasks for which they have privileges for. So even if you create your local user and put him on the Exceptions list, the user won’t be able to connect unless you give him a privilege.
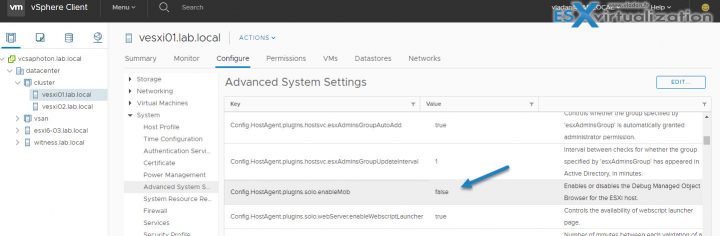
Control access to hosts (DCUI/Shell/SSH/MOB)
You can control the access to the DCUI/Shell and SSH. The MOB is the managed object browser (MOB) and provides a way to explore the VMkernel object model. vSphere 6.0 and later has, the MOB is disabled by default because it could be exploited by hackers.
To Enable MOB:
Select host > Advanced System Settings > Advanced > Config.HostAgent.plugins.solo.enableMob > modify the value.
Security of ESXi hosts is manageable through vCenter server, but also on per-host basis, if you have hosts which are not attached to vCenter.
Restrict administrative privileges
Not all administrator users must have the Administrator role. You might want to create a custom role with the appropriate set of privileges and assign it to other administrators. Users with the vCenter Server Administrator role have privileges on all objects in the hierarchy.
Follow the principle of least privilege. Clone and customize role for nodes you need, and then assign this role to administrators.
Being secured but not too “locked”, have a good balance between security and manageability. Making any changes to the security of the vSphere environment might have perhaps large impacts on the manageability of the environment for you and your team. You should always analyze your needs, your risks, and your requirements. Then change the security of your environment.
To become VCP-DCV 2019 certified you have 3 different choices of exam:
- Professional vSphere 6.7 Exam 2019
- VCP6.5-DCV: VMware Certified Professional 6.5 – Data Center Virtualization exam (our VCP6.5-DCV Study Guide Page which is complete)
- VCP6.5-DCV DELTA: VMware Certified Professional 6.5 – Data Center Virtualization Delta exam
Note: You must be VCP5, or VCP6. If, not, you must attend a class and you have no “Delta” exam option.
Use the official documentation as well as your home lab for the study. Follow the progress of the VCP6.7-DCV Study Guide page for further updates.
This was a really interesting topic today: VCP6.7-DCV Objective 7.4 – Configure host security. We'll continue to cover additional topics until we'll fill completely every single topic required for VCP-DCV 2019 certification.
This, however, does NOT mean that you only rely on our guide when it will be completed.
More posts from ESX Virtualization:
- Cool Free VPN Server Software SoftEther VPN
- What is The Difference between VMware vSphere, ESXi and vCenter
- How to Configure VMware High Availability (HA) Cluster
- What is VMware Orchestrated Restart?
- What is VMware Platform Service Controller (PSC)?
- How To Reset ESXi Root Password via Microsoft AD
Stay tuned through RSS, and social media channels (Twitter, FB, YouTube)