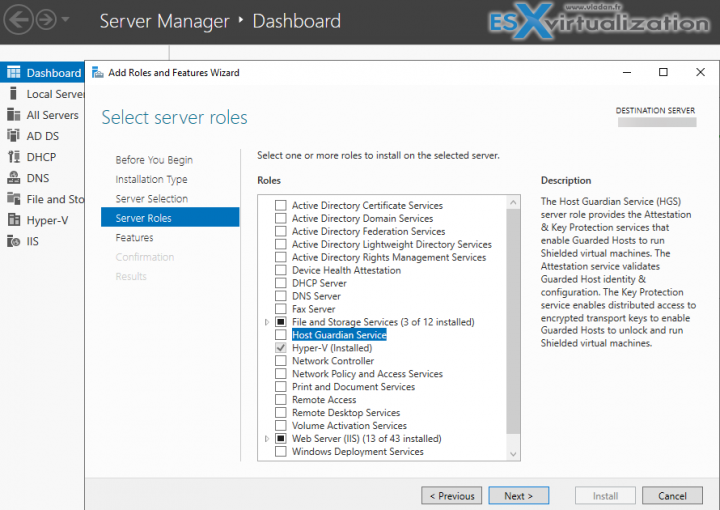
I stumbled across this by reading about Windows Server 2019, it is a Host Guardian Service (HGS), which is responsible for providing attestation and key protection services that enable Hyper-V to run Shielded virtual machines.
This “Host Guardian Service” (HGS) was introduced in Windows Server 2016 actually, and since that time, it's possible to run shielded VMs (VMs using BitLocker to protect their disks). BitLocker keys are needed to boot the VM and decrypt the disks are protected by the shielded VM's virtual TPM.
Shielded VMs protect virtual machines from compromised or malicious administrators in the fabric, (ex. storage admins, backup admins, etc), by encrypting disk and state of virtual machines so only VM (or tenant admins) can access it.
For HGS, It's recommended to separate the roles and as such an HGS admin role has been introduced, as well as HGS Reviewers, which only allows users the right to audit existing policies. They cannot make any changes to the HGS configuration.
HGS admins choose which Hyper-V hosts are authorized to run shielded VMs and manage the certificates necessary to start up shielded VMs. The recommendations from Microsoft are very simple and basically says that domain admin and HGS admins should be two different persons (with two different accounts):
It is recommended that you limit the overlap between the admins of your HGS (including the domain to which HGS is joined) and Hyper-V environments. By ensuring no one admin has access to both systems, an attacker would need to compromise 2 different accounts from 2 individuals to complete his mission to change the HGS policies. This also means that the domain and enterprise admins for the two Active Directory environments should not be the same person.
The notion of Guarded fabric
We have this new term which goes hand in hand with HGS. A guarded fabric consists of one Host Guardian Service (HGS) – typically, a cluster of three nodes – plus one or more guarded hosts, and a set of shielded virtual machines (VMs).
You can have a look at all the necessary workflow for the deployment here. (there are quite a lot of task to do). Basically, what you need to do is:
- Installing Host Guardian Service (HGS) Role
- Configure HGS Server (via PowerShell)
- Authorize Guarded hosts in HGS
- Configure TPM Policies
- Configure HGS client
It's very well documented in Microsoft documentation, so if you're planning to harden your Hyper-V environment, you might want to read the whole details and plan ahead. Ther are quite a few
Prerequisites
-
Hardware: HGS can be run on physical or virtual machines, but physical machines are recommended.
If you want to run HGS as a three-node physical cluster (for availability), you must have three physical servers. (As a best practice for clustering, the three servers should have very similar hardware.)
-
Operating system: Host key attestation requires Windows Server 2019 Standard or Datacenter edition operating with v2 attestation. For TPM-based attestation, HGS can run Windows Server 2019 or Windows Server 2016, Standard or Datacenter edition.
More Links from Microsoft:
- Video: How to protect your virtualization fabric from insider threats with Windows Server 2019
- Video: Introduction to Shielded Virtual Machines in Windows Server 2016
- Video: Dive into Shielded VMs with Windows Server 2016 Hyper-V
- Video: Deploying Shielded VMs and a Guarded Fabric with Windows Server 2016
- Blog: Datacenter and Private Cloud Security Blog
- Overview: Guarded fabric and shielded VMs overview
More from ESX Virtualization
- VCP6.5-DCV Objective 5.2 – Configure vSphere DRS and Storage DRS Cluster
- Windows Server 2019 What's new?
- ESXi Free vs Paid – What are the differences?
- How To Reset ESXi Root Password via Microsoft AD
- How to Patch VMware vCenter Server Appliance (VCSA) 6.7 Offline
- How To do a Dry Run of an esxcli Installation or Upgrade on VMware ESXi
- Veeam Availability Console Released (VAC)
Stay tuned through RSS, and social media channels (Twitter, FB, YouTube)