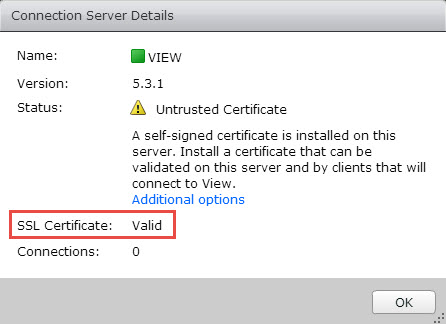
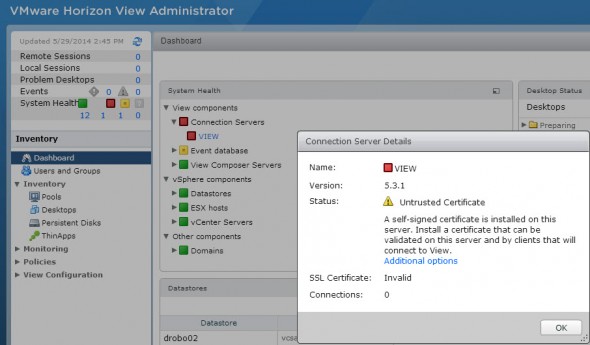
VMware Horizon View Connection Server SSL Certificate (auto-signed) isn't valid and you find yourself with a nice error when you open the VMware view administration web console. It says that the certificate is untrusted and that you have to install a valid (not a self-signed) SSL on this server.
So you'll have have a valid certificate. You have two options:
1. Commercial certificate
2. Self-signed certificate with Microsoft certification authority, which you can add as a role to one of your VMs in your domain.
VMware recommends using valid SSL certificates issued by a valid Certificate Authority (CA) like a public CA such as GoDaddy, Verisign, etc.When you plan your View deployment, you should know if you'll be using any non domain joined devices and (or) if there will be some mobile devices. If there will be, you have to make sure that all the non-domain PCs you use to connect to your View desktops did the import of the CA Root certificate into the Trusted Root Certification Authorities store.
Using SAN certificate (Subject alternative names) might also be the way to go if you planning large View deployment with more than one connection server.
Screenshot from the Dashboard without an option to accept the default self-signed certificate for Horizon View Connection Server.
I have tested the VMware Certificate Automation tool for vCenter installation, but it's still quite lengthy process. The tool can be used to automate the process of uploading certificates and restarting the different components of vCenter, but on the list of the vCenter components the Horizon View connection server is not present, as Horizon View is standalone product. (Note that the tool was recently updated, to 1.0.1 version which automates a bit more the process.)
My lab has the view composer and vCenter server on the same VM and I'm only using single View connection manager server. No security server. The setup don't differ from the steps I've written for View 5.0. You can find the whole serie of how-to setup VMware View in a lab here. The only thing which is causing “a problem” now with View 5.3.1 Connection Server – the self-signed SSL certificate.
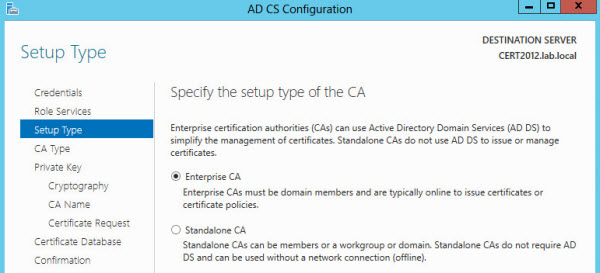
Create Certificate Template with Active Directory Certificate Services. (AD CS)
First, install the role and reboot the server. In my case I'm using Windows Server 2012 AD CS, but you can also use W 2008 or 2003 depending on your environment.
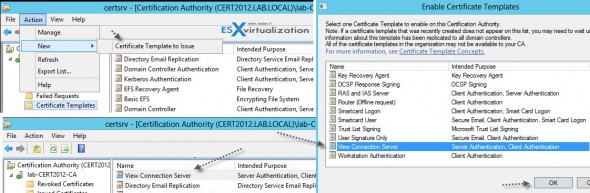
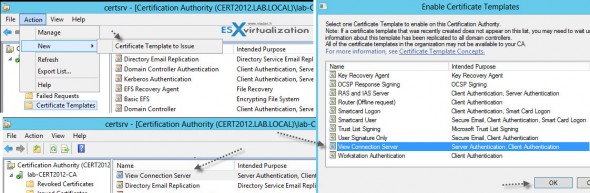
Launch the AD CS console and right click the “Certificate Templates” > and then Manage > to bring up the second console called “Certificate Templates. Check the screenshot below.
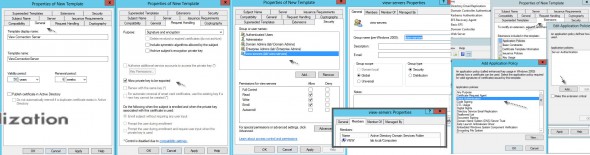
Once done click the Duplicate Template on a Web server template. We're doing this to obtain an option to request web server certificate in addition to the only one default option – computer. You should also:
- create a security group (I called mine view-servers) in your AD and put your View connection server in this group. Add this group to the Security Tab on the properties of the new template and give this group a Write and Enroll permission, in addition to the default read permission.
- As a compatibility, I've selected 2003
- Allow private key to be exported
- Add client authentication to the list
- 50 years of validity
- 4096 as an encryption
Click to enlarge to see the details…
Then, expand the base certificate console, click the menu Actions > New > Certificate Template to issue.
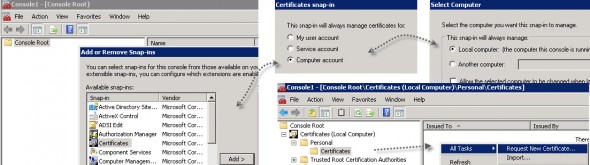
- Now go to your View connection server > launch new mmc and add/remove new snappin for local computer account.
- local computer
- Launch the console and select Certificates > Request new certificate
Then follow the assistant, click on the More Information is required to enroll for this certificate…and enter the common name that you want to use.
- Enter the DNS details
- General tab needs to have “vdm” as a friendly name
Click enroll…And check the view admin dashboard for results…
Then go and export the created certificate from the Personal > certificates folder.
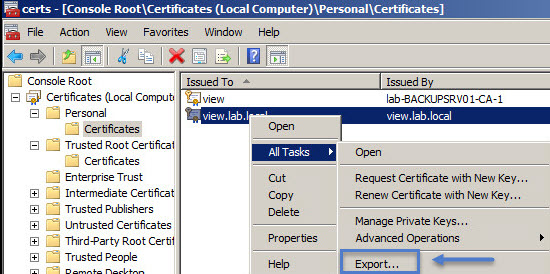
Save the file with some name with *.cer extension.
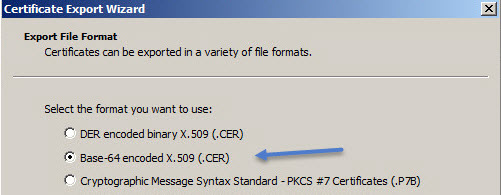
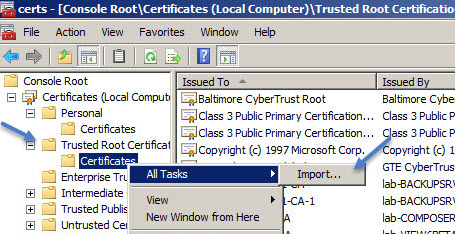
Once you have the file, you'll need then to import the certificate into a Trusted Root certificate store:
That's it! you're done.
The easiest way might be, for lab testing, to create and import certificates before installing View 5.2 ,like this it will use the signed certificate instead of creating one. If
VMware Documentation:
https://pubs.vmware.com/view-52/topic/com.vmware.ICbase/PDF/horizon-view-52-obtaining-certificates.pdf
https://www.vmware.com/files/pdf/view/VMware-View-Evaluators-Guide.pdf
Excellent how-to's:
- With 2008 as a CA – https://my-virt.alfadir.net/2012/11/the-simpliest-way-to-create-view-connection-certificats-with-active-directory-ca
Wrap up:
Certificates are pain. This tutorial helped me to validate the installation and questions I had about View 5.2 certificates. We saw that even if the composer self-signed certificate error can be accepted and the green light let's you go through, its not the same for the View connection server. So the Microsoft PKI is a must as the default View connection server certificate isn't accepted. It's logical as VMware want us to use real , commercial certificates. As a result, if you want to avoid that the only way is to build an enterprise root PKI, create (clone) your own template and then issue a request. This validation process was done mostly for my own purposes, to test it on on the latest Microsoft Windows Server 2012. If you find it useful, just share.
The full serie – VMware View 5 Install, configure – How-to in my lab :
- VMware View 5 Install, configure – How to do a simple lab setup
- How to install Database and ODBC for VMware View
- How-to install VMware View Connection Server
- How-to install VMware View Composer
- How to install VMware View Agent in the Virtual Desktop plus more
- How to create desktop pool in VMware View
- The first connection to a desktop pool
- VMware View – Virtual machine with Input Specification already exists error
- How to Optmize the Master Desktop Image for VMware View
- VMware View Video for SMB
- How-to configure VMware View Persona Management
- How-to remove linked clones reference from composer database video
- VMware Horizon View Connection Server SSL Certificate How-to – this post


Hi Vladan
Thank you for posting an useful article , I have one question regarding Horizon view 6.2 environment where I have deployed a load balancer with SSL offloading and in my View Admin Dashboard the 2 connection shows as invalid and unstrusted certifcate .
How could I solve this
This is definitely an article written by someone who doesn’t understand certificates. Please do not follow this. It may “work,” but it is the wrong way to go about doing this.
Oh dear, this post is from 2013. Imagine that. My apologies -:).
Actually, have you try Horizon view direct connection ? I did try it in ver 7.4 and earlier and the blast web acces was working fine. But i did install the same way with ver. 7.9 and 7.10, but blast don’t work anymore. Is there a new requirement or so ? Over win10 it don’t work.. but also on win8.1… Did also try to remove a 7.3 and put 7.9.. but still. thanks in advance