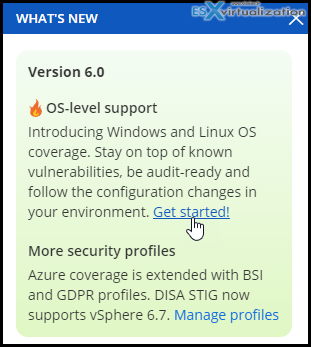
Runecast 6 has introduced a new feature allowing you to stay protected and in compliance at the host level, but also at the OS level. This support is available through agents deployed inside the Guest OS. So far some Windows and Linux OSes are supported but the plans are to extend the support for a larger variety of different OS.
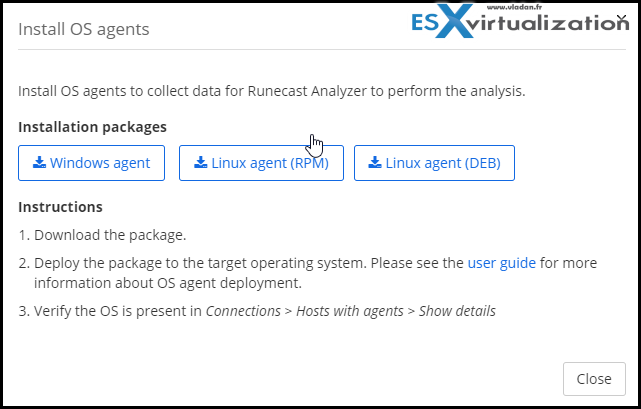
If you have a large number of agents to deploy, you can use GPO Within the Windows environment. On Linux systems, you can use Ansible. The steps are described within the Runecast's user guide available to you locally when you're testing the solution.
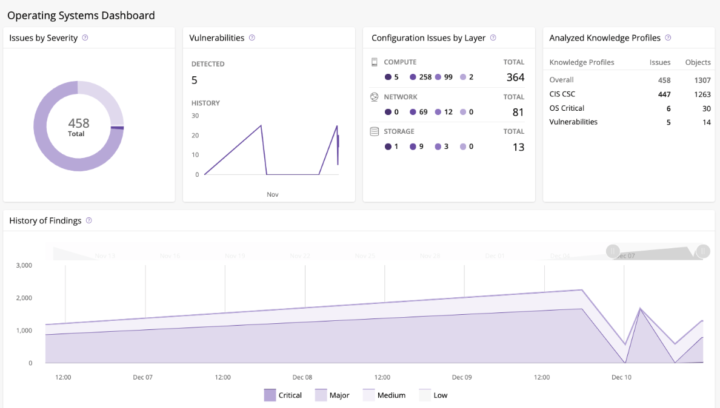
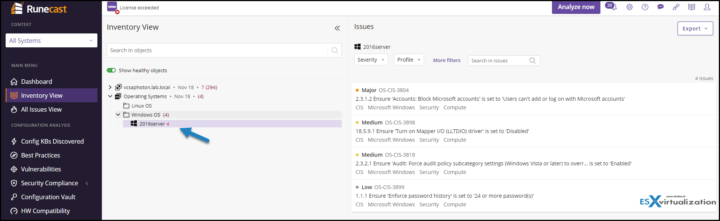
Once you have those agents deployed, you can scan your VMs and get recommendations. Runecast 6.0 includes CIS benchmark certificate for Windows Server 2016 and Red Hat Linux 8. There are approximately 350 rules preconfigured in the Runecast, but those numbers will grow up with the definition updates.
You'll be able to track for your Windows or Linux OS, Configuration Drift Management. Also, you will be able to take advantage of Vulnerability Assessment capabilities. Both of these features can be used for bare-metal installs and virtual installations because a small, lightweight agent is deployed into those systems..
Operating Systems (OS) Analysis consists of two components:
- OS analysis service running on Runecast Analyzer appliance,
- OS agents running on operating systems, collecting data, and reporting to OS Analysis service.
How to Activate OS-Level analysis
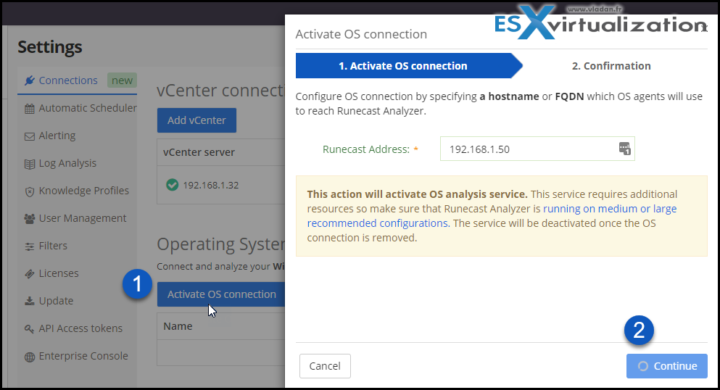
In order to activate the feature (not enabled by default), you'll need to set up a connection allowing the agents to send information back to the Runecast's appliance. The connection will ask you about Runecast's hostname or FQDN. Like this, the settings will be deployed along with the agents to the target OSes.
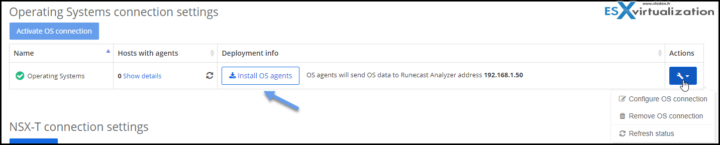
First, connect to the Runecast appliance via the UI and go to Settings > Connections > Go all the way down and where is the Operating Systems connection section click Activate OS connection button.
You'll see a pop-up window like this. Enter the FQDN of your Runecast and click continue.
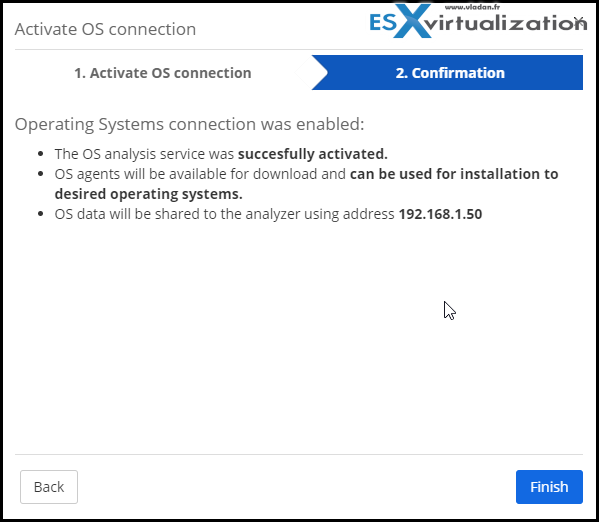
After validation, you will be directed to a page where you can download the agents. You can still access the page when clicking the “Install OS agents” button within the connection section of the configuration.
Once the agents are installed it is possible do execute a validation. You can have a look and validate they can reach Runecast Analyzer appliance. Just go to the “Registered OS agents” view from the “Operating Systems connection” section.
You should see the numbers.
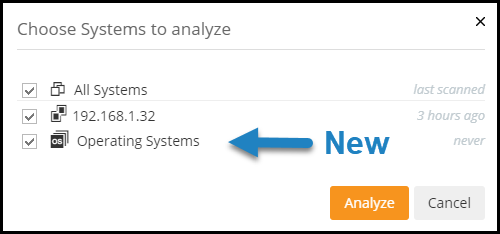
You should see a new section called Operating systems, within Runecast.
This section is under your current Center server system.
Guest OS Analyse within Runecast
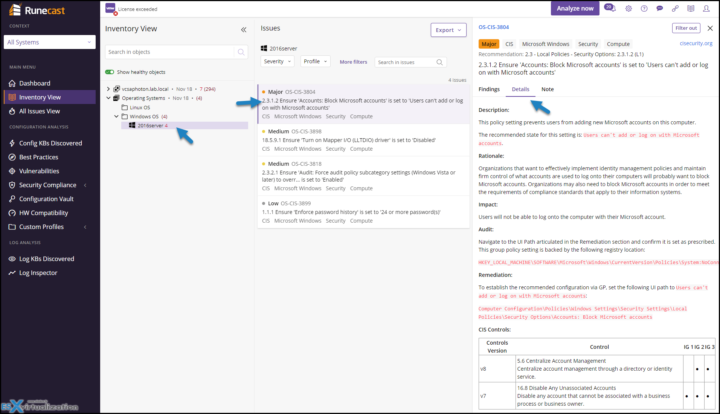
We have successfully deployed one agent to our Windows Server 2016 system. Within the inventory view, you should now see the new addition – Operating Systems.
So when you click the Analyze Now button to trigger manual analyses of your environment, you should see some vulnerabilities showing up there. I have done a test on an unpatched 2016 server so I obviously found some.
Note: This test was done with the beta of the software, so only a few vulnerabilities were found. In the final product release, you'll find much more. Also, the main limitation in the OS-level support within the Beta is the number of automated rules available for each of the categories. This coverage will be significantly increased in the GA release.
Selecting the first problem opens a detailed view where you can find more about this misconfiguration.
In order to follow up best practices, follow different security profiles and recommendations.
Final Words
Runecast 6 is a major release of the software vendor up to date. The new take on security of all systems (not only hosts but also OS) is another step forward to a product that has been used mostly by VMware admins so far. We will see the security threads becoming a major problem in the IT industry. The recent Apache Log4j flaw, a Java library for logging error messages in applications, is a perfect example that security holes, and especially those in Open-source software might become the main vector of attacks. We have seen that Microsoft and Windows systems took the threads seriously for several years and that updates are pushed on a regular basis. But who is pushing security updates for open-source applications? Volunteers working for free during their spare time.
That's why having a single pane of glass a security monitoring appliance, that Runecast is clearly becoming, is a good example of a product that allows you to keep your infrastructure optimized following best practices and KB articles, and also secure by following security advisories and KBs. The detection and reporting is automatic so all admin has to do is on regular basis, follow the recommendations given by Runecast software and reconfigure and patch the systems which needs it.
Runecast also helps with upgrades. It shows you the compatibility of your hardware against the VMware HCL. It runs a rapid, automated analysis using the latest HCL for your servers and I/O devices.
AWS Cloud, Microsoft Azure, Kubernetes, Pure Storage (on vSphere), SAP HANA (on vSphere), VMware Cloud on AWS, VMware vSphere, vSAN, NSX-T, NSX-V, Horizon, Cloud Director and now OS systems (Windows and Linux) are part of the game. Runecast 6 has expanded also the Azure compliance checks to include both BSI IT Grundschutz and GDPR. And our DISA STIG compliance extends now to VMware ESXi 6.7 as well.
Log4Shell Vulnerability Scan
Runecast offers the possibility to detect this issue within your environment. Simply go to this page and request a free scan. You'll be offered a 7 day Runecast trial for unlimited assets. Please note that this applies only to qualified organizations so putting in some erroneous information won't cut it. I'd imagine that trying it with some free e-mail accounts won't be useful and most likely rejected as well. So please don't do that.
More about Runecast on ESX Virtualization
- Runecast can help to detect vulnerability in Apache Log4j Java library
- vSphere Upgrades easier now with Runecast
- Track configuration changes in your vSphere Environments with Runecast Configuration Vault Feature
- Runecast 5.1 delivers Remediation to VMware vSphere customers
- Runecast Analyzer 4.5 Adds Kubernetes Checks and More
More posts from ESX Virtualization:
- vSphere 7.0 Download Now Available
- vSphere 7.0 Page [All details about vSphere and related products here]
- VMware vSphere 7.0 Announced – vCenter Server Details
- VMware vSphere 7.0 DRS Improvements – What's New
- How to Patch vCenter Server Appliance (VCSA) – [Guide]
- What is The Difference between VMware vSphere, ESXi and vCenter
- How to Configure VMware High Availability (HA) Cluster
Stay tuned through RSS, and social media channels (Twitter, FB, YouTube)

Hi Admin,
Your Article always be very Informatic and helpful for me. My humble request to you please provide a Dark mode option on your website. so me and other’s also can read more comfortibly at night. I hope you understand what i try express here. And I expect you do this as soon as possible.
Thanks