In this post we'll try to give you some simple guidelines and tips tips how to secure your backups, your backup infrastructure with your storage repositories, backup servers etc. Those tips can be applied to existing backup infrastructure or on a new deployment of backup software. We're slightly biased towards Veeam Backup and Replication software, but this is only because “It Just Works” however those tips are applicable to any backup software on the market. -:)
Protection of your repositories where your backups are stored, your generated backup files grow there and has to be protected against hackers or an “inside man” on your network. Implementing the least privilege is crucial nowadays because you can't trust anyone.
Your backup server has to become a fortress. A house into which one cannot break. Or if they do, you should be notified. BTW, have you ever thought of installing some software or configure your backups server to send you a notification when some weird activity goes on? When someone logs on outside of business hours or when someone is trying to bruteforce an admin account?
You can be a certified engineer or simple admin without certification, the tips are for everyone. If you know inside out of your existing installation and you have probably implemented most of those tips, simply skip this post and share it through your social network.
Secure Your Backup Architecture itself
Recommended Veeam Backup server is the installation on dedicated hardware. Physical Windows Server. Note that you can also use Windows 10 machine and format the local backup repository as NTFS but you'd lose the benefit of ReFS ( which now works) and which allows you to do some significant space savings because of
A Dedicated Local Backup account – Veeam backup server should be outside your Microsoft domain. You should create a dedicated backup account which will be in the Local User and Groups. I assume you know how to do that. If not simply go and fire CMD console and type compmtmt.msc to open computer management console > go to Local Users and Groups > open Users folder > right-click in Users window > Create New User.
Connect as this user to your backup server and configure storage repositories etc by using this account. Use a strong password for this account.
Make sure the Veeam server has enabled properly and configured the Windows firewall.
Make sure you keep the OS patches current and up to date, as well as your Windows AV/Malware protection software (if using other than the Windows one).
Any SMB / NFS / Linux remote repositories (if not configured on the backup server itself) should have ACL security that has ONLY the service account defined that Veeam will use to connect to it. Nothing else!
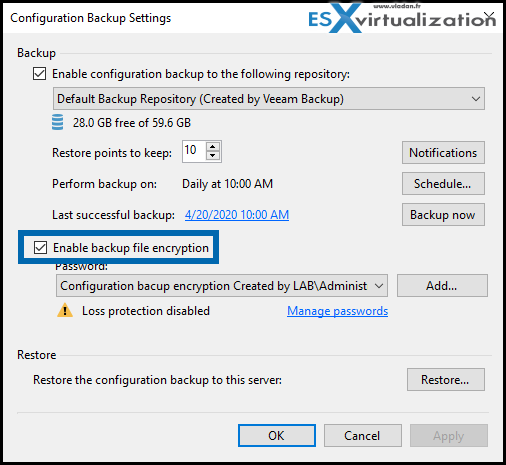
Use a password on your Veeam Configuration backup. Configure the location for the backup to one of those SMB destinations that are protected.
Encrypt your backups, configuration backups (including the credentials)
Veeam backup server stores credentials that are encrypted. You can, additionally, store the configuration backup (with those credentials) as an encrypted file. If you configure the encryption for configuration backup, the credentials stored in Veeam are not readable without the encryption password…
Encrypting your backups might not protect you for the inside man attacks, but it will protect you for malware attacks. However think twice before activating it, because it is very powerful.
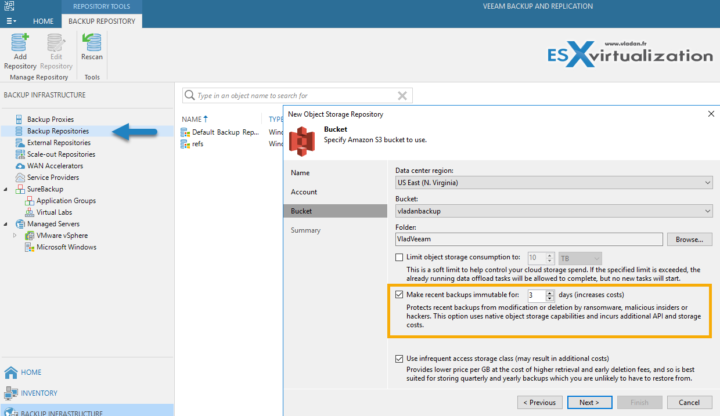
Cloud Repository for Backup Copy jobs with Immutability feature (a Must)
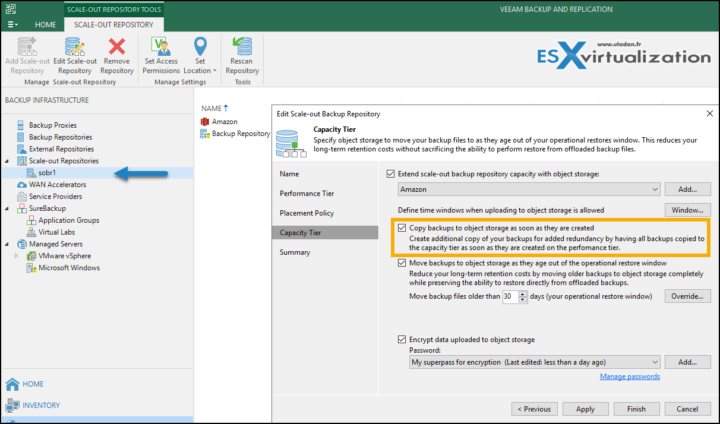
Veeam 10 has a capacity tier enhancement where you can have all your backups to be copied to the object storage once they are created on your on-prem storage, you simply check this box within the settings of your SOBR repository.
What is SOBR repository?
This is basically multiple repositories configured as Veeam Scale-Out Backup Repository (SOBR). Within the UI you'll see a single repository totalizing the capacity of the multiple repositories connected to your backup server.
Within the SOBR you can configure to copy backups to object storage as soon as they are created. This can be Amazon, Azure or any other cloud storage where you can configure Immutability feature. Perfect to fight ransomware. This feature has been added recently to Veeam and we have written a detailed article on how does it looks like at Amazon. (the Immutability feature configuration must be done at Amazon)
Screenshot from the lab…
Now, you might have a question. What if there is a malicious admin which changes back the immutable backups to non-immutable (he/she unchecks that box). What's gonna happen? Will all the backups protected by the object locks become vulnerable again right after? Or, there this logic wants that the original period marked as immutable is followed to the end making the step simply useless. And so no backups of the last 3 days cannot be deleted.
The reply is No because when you enable the Compliance Mode, this mode cannot be disabled by any user, including the root account. (compared to Governance mode which can be disabled by AWS accounts that have specific IAM permissions.
Cloud Connect, Passwords and more…
Passwords for Cloud Connect are stored into Veeam backup server itself and the repository is not visible in any other place in the Veeam console. The cloud repo is not visible or reachable in the local network. The malware would need to grab credentials from the Veeam server and seek for the connection that Veeam does have for cloud connect. It's not a simple RPC/SMB connection over the network. The malware would have to be “designed” to do that.
If you're using a NAS device on your network, for local repos, it's a good idea not to register it over the network via Active Directory or Workgroup, but only use a dedicated user/password that is NOT used anywhere else. Only via the Veeam backup server. Because when you register this device in Veeam, you can be 100 % sure that only Veeam software can access this device.
By using dedicated passwords for the Veeam backup server, the Active Directory (AD) admin does not have access to your backups (if this is not the same person).
3-2-1 Backup Rule
What Is it? Basically saying that you should store the copy of your backup not only on the primary location, but also on secondary location (remote datacenter/cloud), and third on a different media (tape).
One of the settings you have on SOBR is that you can copy backups to object storage as they are created.
This is just perfect for 3-2-1 backup rule! You’ll be able to have one full copy of your data off-site, and not create a separate copy job for it -:). When running your backup job and creating local backup files, they’re immediately copied to the capacity tier, within the same job, and nobody (including you) is able to delete them.
Image from the lab…
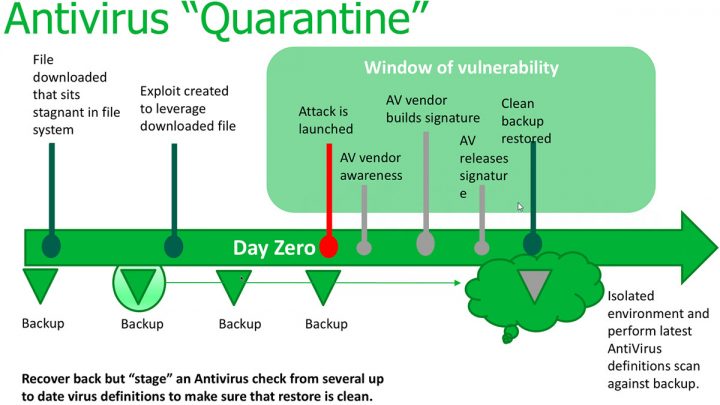
AntiVirus Quarantine
When you look at ransomware scenarios. Someone downloads an infected file and it's a day zero, so your antivirus don't know that the file has been infected. Then, few days later, after the antivirus definitions get an update, the file will be signaled by your antivirus software. But how about your backups? Well, your backup files will be obviously infected.
With this you'll get the option to restore to an isolated environment > clean the system > then restore to production.
Without this, you would restore including the infected file (which might have possibly acted like a “time bomb”). So obviously risky.
Final Words
This is no mean all you can do to protect your backup server against malware and reinforce security. With different architectures, you'll need different tips and different techniques of protection. The key is separation. Separation of backups from the production environment is N° 1 on the list. You can then treat the backup server entity as a whole without changing security policy for your whole company.
- Veeam Scale-Out Backup Repository
- What is Veeam Universal License?
- How to Install and Configure Veeam Backup and Replication 10 Community Edition
- Fight Ransomware with Veeam 10 Immutability Feature
- What is Veeam Copy Mode Feature?
Links:
<<<<< Veeam Backup and Replication v.10 – Trial >>>>>
More from ESX Virtualization
- Veeam Backup Community Edition – Download Now
- Fight Ransomware with Veeam 10 Immutability Feature
- What is Veeam Copy Mode Feature?
- What are Open VM Tools and How to use them?
- VMware API Explorer Is a Free Built-in Utility in VCSA
- V2V Migration with VMware – 5 Top Tips
- ESXi Free Version – 3 Ways to Clone a VM
- What is ESXi Compatibility Checker?
- How To SlipStream Latest VMware ESXi patches into an Installation ESXi ISO File
You might want to check our Free Tools page where you can find VMware utilities, but also utilities for Microsoft systems or other “Swiss Knife” software there.
Stay tuned through RSS, and social media channels (Twitter, FB, YouTube)