Another post which is part of our Community Study Guide page. This post, VCP-DCV on vSphere 8.x Objective 1.9 – Recognize methods of securing virtual machines, is part of our VCP8-DCV Study Guide Page. (work-in-progress)
The VMware Exam page is here on VMware’s website. The official code for this exam is 2V0-21. 23. The topic is part of the Official VMware blueprint. (direct link to the PDF). So, let's get back to the topic.
Virtualization is one of the most popular technologies in modern IT infrastructure, offering numerous benefits such as improved resource utilization, scalability, and flexibility. One of the most widely used virtualization platforms is VMware vSphere, which enables the creation and management of virtual machines (VMs) on a single physical server. While virtualization provides many advantages, it also introduces new security challenges that need to be addressed.
Enable Encryption – Encrypting virtual machines is one of the most effective ways of securing data stored on them. You can use the built-in Key Management Server (KMS) that is free, or you can add your KMS if you already have one. With VMware vSphere 8.0, it is possible to encrypt virtual machines at rest and in motion. Virtual machine encryption is a feature that encrypts virtual machine files and virtual disks, making it harder for attackers to access sensitive data. Additionally, network encryption is another feature that encrypts data in motion between virtual machines and networks, which prevents attackers from intercepting the data.
Use Virtual Machine Isolation – You can isolate VMs running by segregating network traffic via VLANS. VMs can run also in a sandboxed environment that isolates them from other virtual machines and the host system and from the internet. By isolating virtual machines, administrators can prevent unauthorized access to sensitive data and reduce the risk of malware spreading from one virtual machine to another.
Implement Access Controls – Access control is a fundamental security measure that limits access to resources based on the user's identity and privileges. VMware vSphere 8.0 provides several access control mechanisms, including role-based access control (RBAC) and virtual machine permissions. By implementing access controls, administrators can restrict access to virtual machines, preventing unauthorized users from accessing sensitive data or making changes to virtual machine configurations.
Activate or Deactivate UEFI Secure Boot for a Virtual Machine – UEFI Secure Boot is a security standard that helps ensure that your OS boots using only software that is trusted by the PC manufacturer. For certain virtual machine hardware versions and operating systems, you can activate secure boot just as you can for a physical machine.
Apply Security Patches and Updates – More than every, this is crucial today, when zero day vulnerabilities and ransomware are spreading very fast. Security patches and updates are crucial in maintaining the security of virtual machines. VMware regularly releases security patches and updates for vSphere, which include bug fixes and vulnerability patches. By applying these patches and updates, administrators can keep virtual machines secure and reduce the risk of attacks.
Securing Virtual Machines with Intel Software Guard Extensions – vSphere enables you to configure Virtual Intel® Software Guard Extensions (vSGX) for virtual machines. Using vSGX enables you to provide additional security to your workloads
Use Antivirus and Anti-Malware Software – I should not even talk about this one, which is a must. Antivirus and anti-malware software are essential tools in protecting virtual machines from malware and other security threats. VMware vSphere 8.0 supports the use of third-party antivirus and anti-malware software, which can be installed directly on the virtual machines. By using these tools, administrators can detect and remove malware, preventing it from spreading to other virtual machines or the host system.
Use Templates to Deploy Virtual Machines – When you manually install guest operating systems and applications on a virtual machine, you introduce a risk of misconfiguration. By using a template to capture a hardened base operating system image with no applications installed, you can ensure that all virtual machines are created with a known baseline level of security.
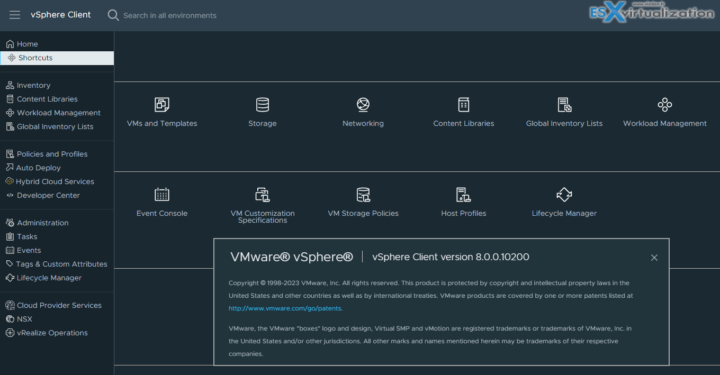
vSphere 8
Deactivate Unnecessary Functions Inside Virtual Machines – Any service that runs in a virtual machine provides the potential for attack. By deactivating system components that are not necessary to support the application or service that is running on the system, you reduce the attack potential
Wrap Up
Virtualization provides many benefits, but it also introduces new security challenges that need to be addressed. In this blog post, we have reviewed at high level several methods of securing virtual machines in VMware vSphere 8.0.
These methods include enabling VM encryption, using virtual machine isolation, configuring virtual machine firewalls, implementing access controls, applying security patches and updates, using antivirus and anti-malware software, and enabling network segmentation. By implementing these security measures, administrators can ensure the security of virtual machines and reduce the risk of attacks.
Hopefully this chapter will help you to study towards VMware VCP-DCV Certification based on vSphere 8.x. Find other chapters on the main page of the guide – VCP8-DCV Study Guide Page.
More posts from ESX Virtualization:
- Homelab v 8.0 (NEW)
- vSphere 8.0 Page (NEW)
- Veeam Bare Metal Recovery Without using USB Stick (TIP)
- ESXi 7.x to 8.x upgrade scenarios
- A really FREE VPN that doesn’t suck
- Patch your ESXi 7.x again
- VMware vCenter Server 7.03 U3g – Download and patch
- Upgrade VMware ESXi to 7.0 U3 via command line
- VMware vCenter Server 7.0 U3e released – another maintenance release fixing vSphere with Tanzu
- What is The Difference between VMware vSphere, ESXi and vCenter
- How to Configure VMware High Availability (HA) Cluster
Stay tuned through RSS, and social media channels (Twitter, FB, YouTube)