Microsoft has confirmed the next major update of Windows 11 and its name is Windows 11 version 24H2. This was somehow expected as Windows 12 development, that some of you were wishing to come, has not started yet.
Windows 11 version 24H2 will bring many new features for end users (energy saver, scrollable quick settings, QR codes for Wi-Fi sharing, support for creating 7-zip and TAR archives in addition to ZIP in File Explorer, Windows protected print mode, voice clarity) but also some components that might be useful for administrators.
The upcoming Windows 11 version 24H2 is still work-in-progress and expect some changes that may be included in the final. Remember, we're still early February 2024.
Table of contents
- LAPS
- SMB firewall rule changes
- The SMB NTLM blocking exception list
- SMB Alternative client and server ports
- More Snap Layouts
LAPS
Those components comes from the Windows Server development, such as SMB protocol changes, improvements to Windows Local Administrator password solution (LAPS) or improvements for Bluetooth and graphics too.
Note: we have done an article about LAPS back in a day on this here , there was a new free utility from Microsoft called Local Administrator Password Solution (LAPS) which enhances a security on domain managed workstations (servers) by managing the local admin passwords in the domain on those systems – not sure it's still works).
Quote:
Today we are releasing Windows 11 Insider Preview Build 26052 to the Canary and Dev Channels.
Insiders in the Canary Channel will receive Build 26052.1000 while Insiders in the Dev Channel will receive Build 26052.1100 (KB5035384) as we test delivery of a full build and a servicing update at the same time. There is no difference between the two of these as Build 26052.1100 does not include any additional code. (Arm64 devices in the Dev Channel will not receive Build 26052.1100.)
The upcoming Windows 11 version 24H2 build will receive some updates that are being developed for Windows 2025 Server, such as changes to the SMB, with SMB Firewall rules.
SMB firewall rule changes
Creating SMB shares changes a longtime Windows Defender Firewall default behavior. Previously, creating a share automatically configured the firewall to enable the rules in the “File and Printer Sharing” group for the given firewall profiles. Now, Windows automatically configures the new “File and Printer Sharing (Restrictive)” group, which no longer contains inbound NetBIOS ports 137-139. We plan future updates for this rule to also remove inbound ICMP, LLMNR, and Spooler Service ports and restrict down to the SMB sharing-necessary ports only.
The SMB NTLM blocking exception list
is part of the changes as well. What is it? There will be a new NTLM blocking feature list (announced in Windows 11 Insider Preview build 25951) supports specifying exception lists for NTLM usage. Admins will be able to configure general block on NTLM usage and still allow clients to use NTLM for specific server that do not support Kerberos (those not joined in AD or are third party servers without Kerberos support).
SMB Alternative client and server ports
The SMB client will support connection to an SMB server over TCP, QUIC, or RDMA using alternative network ports to the hardcoded defaults. Before via SMB, one could only connect via TCP/445, QUIC/443, and RDMA iWARP/5445. Also, the SMB over QUIC server in Windows Server also supports clients that have configuration with different ports than 443. (Note: Windows Server does not support configuring alternative SMB server TCP ports, but third parties such as Samba in Linux do support that).
You can specify an alternative SMB client port using the NET USE command and New-SmbMapping PowerShell cmdlet. You can also completely disable this feature with a group policy.
quote:
The SMB over QUIC client access control feature first announced in Windows 11 Insider Preview Build 25977 now supports using certificates with subject alternative names and not just a single subject. This means the client access control feature now supports using a Microsoft AD Certificate Authority and multiple endpoint names, just like the currently released version of SMB over QUIC.
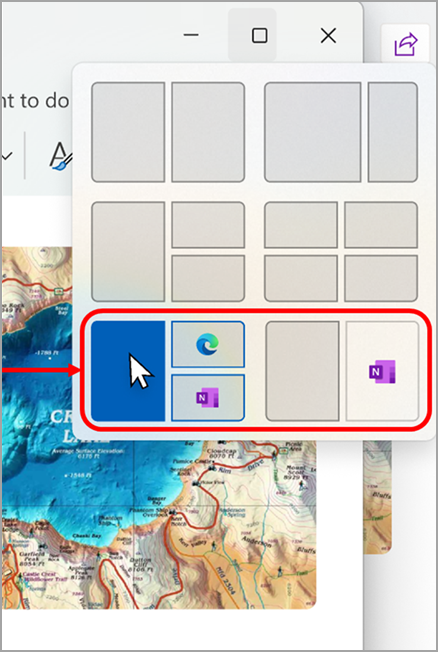
More Snap Layouts
This will be more appreciated by many users with large monitors (including me). There will be new layouts which allows you to snap your Windows apps the way more efficiently and use your desktop space more wise.
Particularly useful when working with many app windows in a single screen. Different layouts are available with many sizes to choose from, so you can get the most from your favorite apps when you are working on specific tasks.
Example from Microsoft below…
Quote:
When hovering over the Minimize or Maximize button on an app (or WIN + Z) to launch the layout box, you will see app icons displayed in various layout options to help recommend the best layout option that works best.
This info comes from Microsoft's blog here.
More posts from ESX Virtualization:
- vSphere Configuration Profiles – How VMware vCenter Server 8.0 U2 Can Simplify and Optimize vSphere Infrastructure Administration
- vSphere 8 U2 Identity Federation with Entra ID/Azure AD – vSphere never sees the users credentials
- VMware vCenter Server Converter 6.4 Released
- VMware vSphere 8.0 U2 Released – ESXi 8.0 U2 and VCSA 8.0 U2 How to update
- What’s the purpose of those 17 virtual hard disks within VMware vCenter Server Appliance (VCSA) 8.0?
- VMware vSphere 8 Update 2 New Upgrade Process for vCenter Server details
- VMware vSAN 8 Update 2 with many enhancements announced during VMware Explore
- What’s New in VMware Virtual Hardware v21 and vSphere 8 Update 2?
- Homelab v 8.0
- vSphere 8.0 Page
- Veeam Bare Metal Recovery Without using USB Stick (TIP)
- ESXi 7.x to 8.x upgrade scenarios
- A really FREE VPN that doesn’t suck
- Patch your ESXi 7.x again
- VMware vCenter Server 7.03 U3g – Download and patch
- Upgrade VMware ESXi to 7.0 U3 via command line
- VMware vCenter Server 7.0 U3e released – another maintenance release fixing vSphere with Tanzu
- What is The Difference between VMware vSphere, ESXi and vCenter
- How to Configure VMware High Availability (HA) Cluster
Stay tuned through RSS, and social media channels (Twitter, FB, YouTube)
